Securing The Future
Falcon Shield CSOC monitoring and analyze phishing activities on networks improving cyber security world through vulnerability disclosure with our accurate expert threat intelligence agents.
24/7 Real-time threat hunting, detection, and response delivered by an expert team as a fully-managed service

24/7 Monitoring
Detection notification and provide details to help you with prioritization and response.

CSOC Collaborate
Working with your team and external point(s) of contact to respond to the detection.

Authorize
We handle containment and neutralization actions and inform you of the action(s) taken.
Stay a Step Ahead of Cyber World Attackers
Solutions by Industry
Cyber Security Solutions
Falcon Real-time CSOC/XDR Threat Hunters proactively protects your environment

FSC Threat Hunting Cyber Security Operation Center Team service make it possible to identify the blind spots generated by each phase of the “kill chain” by comparing them to known Terrorist Tactics, Techniques, and Procedures (TTPs).
We provide a full range of security services and 24/7 monitoring to improve security and upgrade capabilities.
Cyber Defense Services delivered 24/7/365 by our highly skilled Security Operations Team based in Kuwait.
The best way to minimize the effects of a data breach, is to detect it early. While your company may already have certain security measures in place, our Threat Hunting service takes it a step beyond your firewalls and anti-virus.
Our team will manually scan for indicators that tell us if malware or an attacker has been or is currently on the network. This proactive scanning can uncover additional malicious threats that may go unnoticed by standard defenses and can help shrink the gap between breach and identification, therefore reducing the aftermath of a data breach.
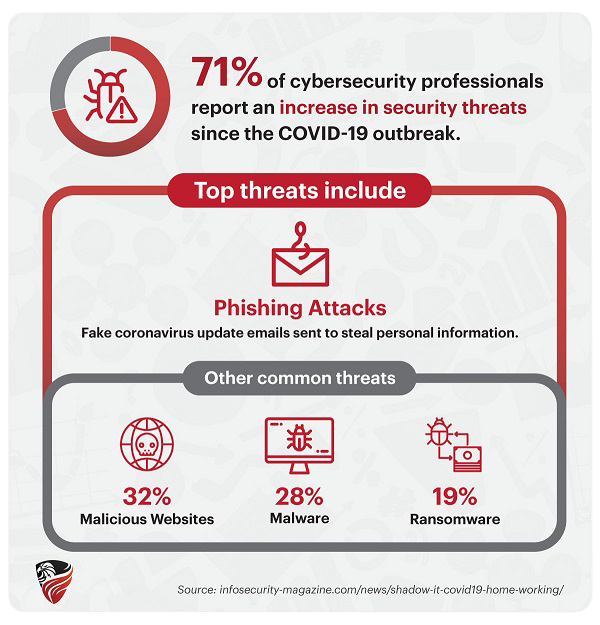
Digital technologies lie at the heart of nearly every industry today. The automation and greater connectedness they afford have revolutionized the world’s economic and cultural institutions — but they’ve also brought risk in the form of cyberattacks.
Firewall Rules examine the control information in individual packets. The Rules either block or allow those packets based on rules that are defined on these pages. Firewall Rules are assigned directly to computers or to policies that are in turn assigned to a computer or collection of computers.
Data loss prevention (DLP) is a strategy for making sure that end users do not send sensitive or critical information outside the corporate network. The term is also used to describe software products that help a network administrator control what data end users can transfer.
Providing a continuous cycle of Penetration Testing combined with Remediation, Vulnerability Management and other Security Tools to protect your Security Posture.
A vulnerability assessment is a systematic review of security weaknesses in an information system. It evaluates if the system is susceptible to any known vulnerabilities, assigns severity levels to those vulnerabilities, and recommends remediation or mitigation, if and whenever needed.
Falcon Shield offers unique cybersecurity trainings courses accredited by and in collaboration/partnership international universities & organization, with focus on building practical capabilities. Moreover, We provide courses on cyber security specializations such as ISO Implementation, Incident Response and Security Operations in order to prepare and empower your cyber security workforce.
Be ready for the future today!
Take Action Against Threats With Falcon’s Real-time Cyber Security Operations Center
Falcon Managed Threat Response of threat hunters and response experts:
![]() Proactively hunt for and validate potential threats and incidents
Proactively hunt for and validate potential threats and incidents
![]() Use all available information to determine the scope and severity of threats
Use all available information to determine the scope and severity of threats
![]() Initiate actions to remotely disrupt, contain, and neutralize threats
Initiate actions to remotely disrupt, contain, and neutralize threats
![]() Provide actionable advice for addressing the root cause of recurring incidents
Provide actionable advice for addressing the root cause of recurring incidents
Recent Posts