PROACTIVE CYBERSECURITY & EVENT MANAGEMENET
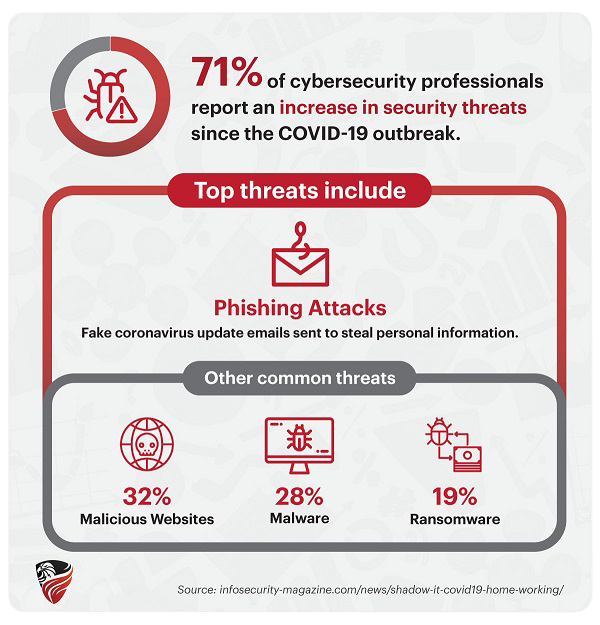
Government organizations and contractors are at even higher risk of attack than Commercial enterprises. When the data you need to protect is so valuable, acting after the breach occurred is too late. Audit logs should be monitored in real-time to identify any potential threat as soon as it occurs, and act proactively before an attack causes irreversible damage or steals valuable information.